The Worm That Lives Inside Your Browser
- Javier Conejo del Cerro
- 26 mar
- 3 Min. de lectura
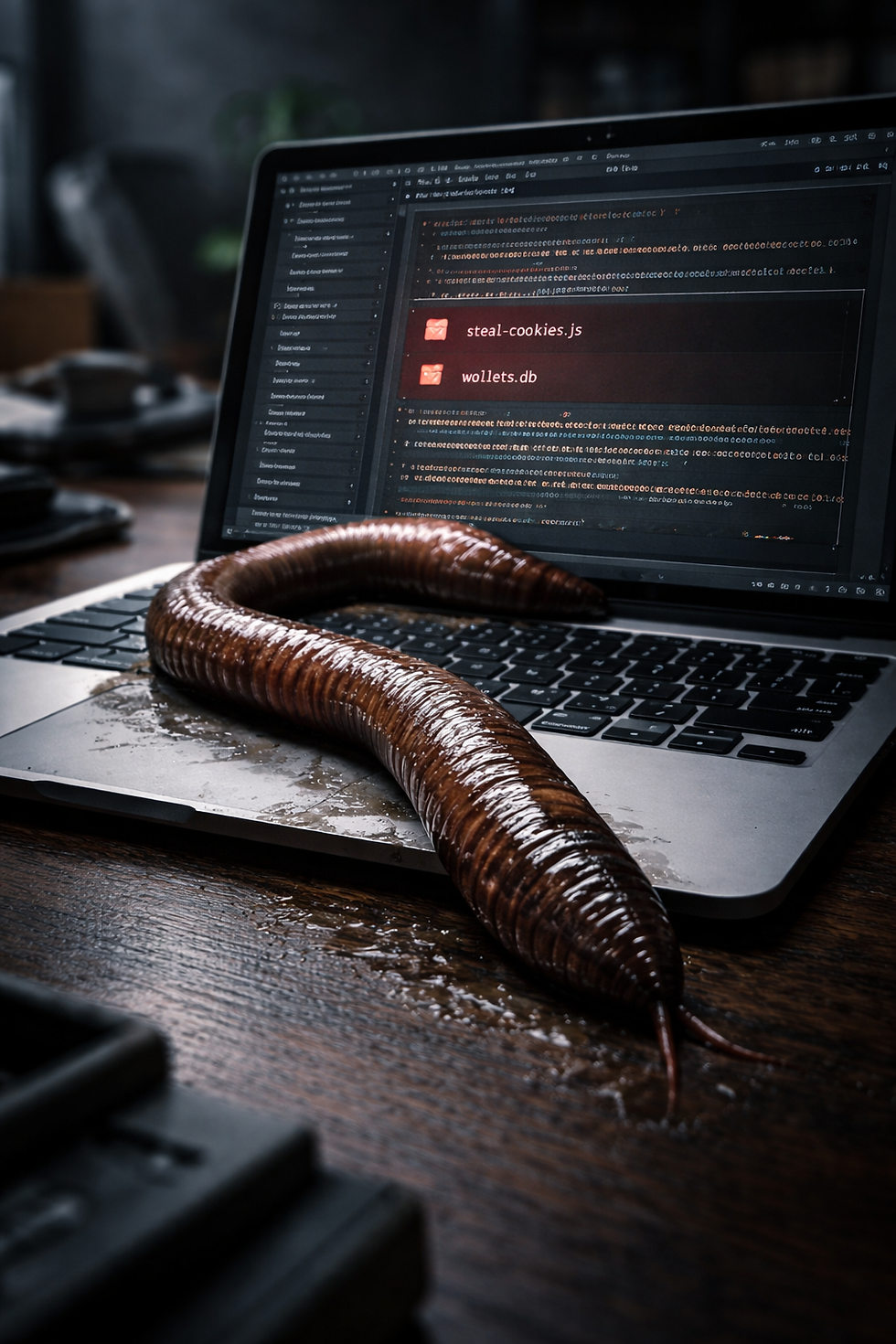
GlassWorm represents a new generation of supply chain malware that doesn’t just infect systems—it burrows into them. By abusing trusted developer ecosystems and leveraging decentralized infrastructure like Solana for command-and-control, the campaign achieves stealth, persistence, and deep visibility into user activity. Like a worm, it doesn’t strike loudly—it spreads, observes, and consumes from within.
Phase 1: Entry & Infection — The First Crawl
The attack begins through poisoned packages distributed across npm, PyPI, GitHub, and Open VSX, or through compromised maintainer accounts pushing malicious updates.
Victims unknowingly install these packages or extensions, often trusting download counts or repository legitimacy. The infection chain is designed to avoid detection, even excluding systems with Russian locales to evade scrutiny.
Once installed, the malware establishes its initial foothold without obvious signs of compromise.
Phase 2: Command Retrieval — Hidden in the Chain
Instead of traditional infrastructure, GlassWorm uses the Solana blockchain as a dead drop resolver to retrieve command-and-control server details.
If needed, it can also fall back to alternative mechanisms like Google Calendar events or distributed hash tables (DHT), ensuring resilience and redundancy.
This decentralized approach makes takedown and detection significantly harder, as the control layer blends into legitimate public infrastructure.
Phase 3: Data Harvesting & Surveillance
The second-stage payload deploys a comprehensive data theft framework:
Keylogging and screenshot capture
Cookie and session token extraction
Browser data exfiltration across Chrome, Edge, Firefox, Brave, Opera, and others
Cryptocurrency wallet targeting, including hardware wallet phishing
A fake Google Docs Offline extension is installed, acting as a persistent surveillance tool. It collects cookies, DOM data, clipboard content, browsing history, and extension lists, and monitors specific platforms like Bybit for session tokens.
All collected data is compressed and exfiltrated to attacker-controlled infrastructure.
Phase 4: Control, Phishing & Persistence
GlassWorm escalates with additional payloads:
A .NET binary that detects hardware wallets (Ledger, Trezor) via WMI and displays phishing interfaces to capture recovery phrases
A WebSocket-based RAT enabling remote command execution, proxying (SOCKS), and hidden desktop access (HVNC)
Persistence is enforced through continuous C2 communication and re-triggered phishing windows, ensuring the victim remains exposed even after interaction attempts to close them.
The campaign expands through new ecosystems like MCP servers, signaling its evolution alongside AI-driven development environments.
Measures to Fend Off
Avoid installing unverified packages, extensions, or MCP servers
Verify publisher identity, repository history, and code integrity
Monitor unusual outbound traffic and blockchain-based C2 patterns
Detect and remove unauthorized browser extensions
Isolate compromised systems and investigate persistence mechanisms
Rotate all exposed credentials and wallet recovery phrases
Use tools like glassworm-hunter for local detection
Educate developers on supply chain threats and trust boundaries
GlassWorm demonstrates how modern malware no longer relies on centralized infrastructure or single-stage execution. By combining supply chain compromise, decentralized C2 mechanisms, and deep browser-level surveillance, it achieves a level of stealth and persistence that is difficult to detect and disrupt.
The use of Solana as a dead drop highlights a growing trend: attackers are embedding their operations into legitimate, decentralized systems, making them harder to trace and remove.
This is not just a malware campaign—it is a shift in how threats operate. The worm doesn’t break in. It is installed, trusted, and allowed to grow.
And once it does, it doesn’t just steal data—it lives inside the very tools users rely on every day.
The Hacker News




Comentarios